Vulnerability Description: Cross-site Scripting (Reflected) - CWE-79
Software Version: 7.0.15
NIST: https://nvd.nist.gov/vuln/detail/CVE-2024-10029
CVSS: 6.1
Severity: Medium
Credits: Claudia Bartolini, Marco Ventura, Andrea Carlo Maria Dattola, Debora Esposito, Massimiliano Brolli
In Eclipse GlassFish version 7.0.15 is possible to perform Reflected Cross-site scripting attacks. Reflected cross-site scripting vulnerabilities arise when data is copied from a request and echoed into the application's immediate response in an unsafe way. An attacker can use the vulnerability to construct a request that, if issued by another application user, will cause JavaScript code supplied by the attacker to execute within the user's browser in the context of that user's session with the application.
Step-by-step instructions and PoC
An unauthenticated remote attacker can create a malicious link that, if it is delivered to the victim (e.g., phishing), can cause JavaScript code execution in the victim's browser and supply some information to the attacker or run arbitrary HTTP Request in the context of victim's session.
Affected Endpoints
• URL: https://[IP]:[PORT]/shared/instanceStatus.jsf
• HTTP GET Parameter: instanceName
Below there is the evidence with the vulnerability details and the payloads used.
Payload used to exploit the vulnerability:
https://[IP]:[PORT]/shared/instanceStatus.jsf?instanceName=%22%20id=%22x%22%20tabindex=%221%22%20onfocus=%22alert(1)%22%20autofocus=%22
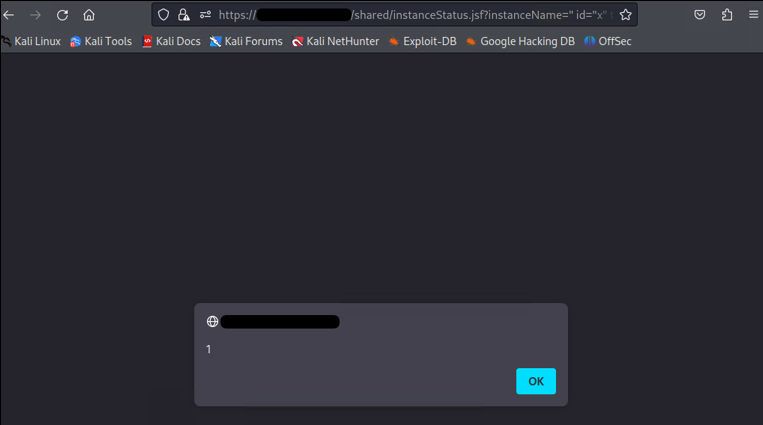
Figure 1: Reflected Cross-site Scripting
Security Impact
An attacker can exploit this vulnerability to extract some information or run arbitrary HTTP Request in the context of victim's session.
Remediation Steps
In most situations where user-controllable data is copied into application responses, cross-site scripting attacks can be prevented using two layers of defences:
- Input should be validated as strictly as possible on arrival, given the kind of content that it is expected to contain. For example, personal names should consist of alphabetical and a small range of typographical characters, and be relatively short; a year of birth should consist of exactly four numerals; email addresses should match a well-defined regular expression. Input which fails the validation should be rejected, not sanitized.
- User input should be HTML-encoded at any point where it is copied into application responses. All HTML metacharacters, including < > " ' and =, should be replaced with the corresponding HTML entities (< > etc).
In cases where the application's functionality allows users to author content using a restricted subset of HTML tags and attributes (for example, blog comments which allow limited formatting and linking), it is necessary to parse the supplied HTML to validate that it does not use any dangerous syntax; this is a non-trivial task.