Vulnerability Description: Reflected Cross Site Scripting - CWE-79
Software Version: 10.x, 11.x, 12.x, 23.x, 24.x, 25.1.x
NIST: https://nvd.nist.gov/vuln/detail/CVE-2025-12454
CVSS: 6.1
Severity: Medium
Credits: Marco Nappi, Mariano Forte, Federico Draghelli, Massimiliano Brolli
Cross-Site Scripting Reflected, an attacker can run arbitrary JavaScript code exploiting unmanaged input.
Step-by-step instructions and PoC
Affected Endpoints
Esss&endTime=19+Jun+2025+09%3A54%3A58.974%22%3Esss&pageNum=1%27%3E%3Csvg/onload=alert
(document.cookie)%3E
svg%2fonload=alert(document.cookie)>&startTime=1750307021463&endTime=1750321421473
Below are the evidences with the vulnerability details and the payloads used.
Payload used to exploit the vulnerability (second example): “><svg/onload=alert(document.cookie)>
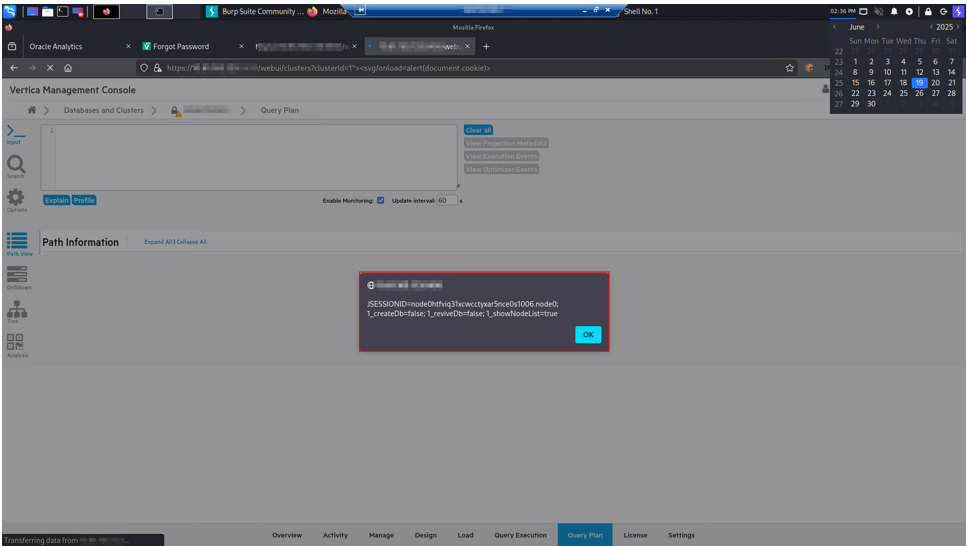
Image 1 - "clusterId” Parameter"
Security Impact
Due to this Reflected Cross-Site Scripting (XSS) vulnerability an attacker can gain the full access to the Databases managed through the web application. Exploiting this vulnerability an attacker can steal the session cookie of any user. Using the stolen cookie an attacker can log into the web application without the user’s password. Once logged the user can use the web application to interact with the database.