Vulnerability Description: Use of Hard-coded Credentials - CWE-798
Software Version: before 2.5.0
NIST: https://nvd.nist.gov/vuln/detail/CVE-2025-9497
CVSS:
Severity:
Credits: Dario Emilio Bertani, Raffaele Bova, Andrea Sindoni, Simone Bossi, Antonio Carriero, Marco Manieri, Vito Pistillo, Davide Renna, Manuel Leone, Massimiliano Brolli
It is possible to extract the passwords used to decrypt the configuration file and the filesystem packet. These passwords are hardcoded in files /tmp/upg/pass.txt (for the first secret key) and /tmp/upg/pass1.txt (for the second secret key).
Prerequisites: access to the local files.
Step-by-step instructions and PoC
Below are the evidences with the vulnerability details.
The upgrade package consists of multiple files:
1. tp4100_mmc_image.tgz: an encrypted archive containing the new filesystem;
2. desc_enc: an encrypted configuration file;
3. preinstall.sh: an encrypted script executed before installing the new filesystem;
4. postinstall.sh: an encrypted script executed after installing the new filesystem.
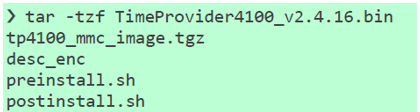
Figure 1
Analysing the upgrade procedure implemented in the binary /usr/sbin/istated, it is evident that the files are encrypted using symmetric encryption and the passwords required for decryption are hardcoded.
The upgrade process can be summarized as follows:
1. The file /tmp/upg/pass.txt is created, and the secret key is written to it;
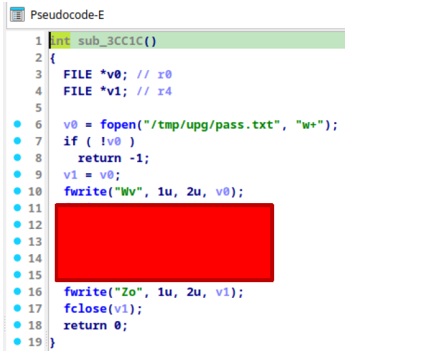
Figure 2 - Evidence
2. The desc_enc file is decrypted using AES 256 CBC with the password stored in pass.txt;
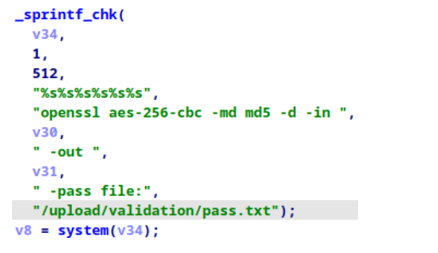
Figure 3 - Evidence
3. Once the desc_enc file has been decrypted, it is parsed to extract the pass-seed value, which is used as part of the password for decrypting the filesystem package;
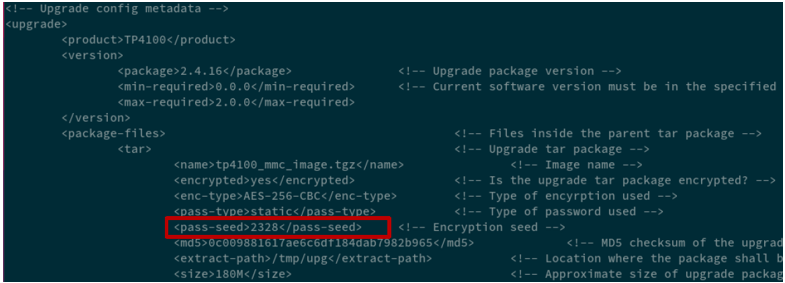
Figure 4 - Evidence
4. The file /tmp/upg/pass1.txt is created, and the second secret key is written to it. This secret key consists of a prefix of hardcoded characters, the pass-seed value extracted from the configuration file, and a suffix of additional hardcoded characters.
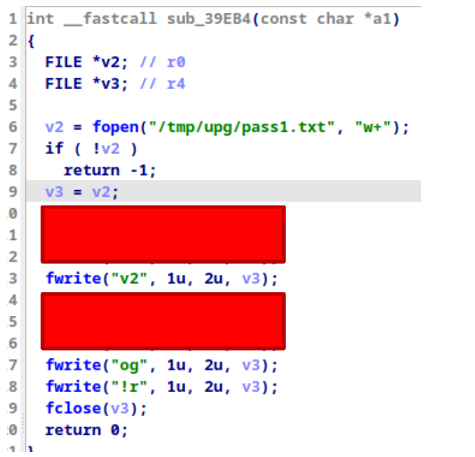
Figure 5 - Evidence
5. Finally, the file tp4100_mmc_image.tgz, preinstall.sh, and postinstall.sh are decrypted using AES 256 CBC with the password saved in pass1.txt.
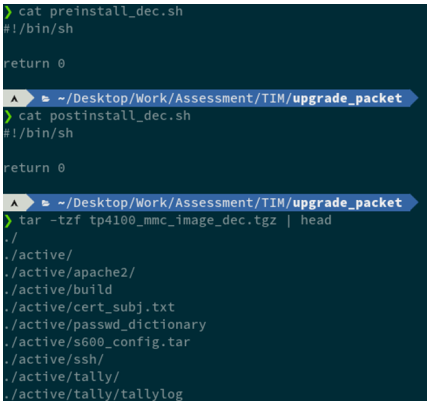
Figure 6 - Evidence
Security Impact
An attacker could extract passwords from the binary decrypting and installing malicious updates.