Vulnerability Description: Download of Code Without Integrity Check - CWE-494
Software Version: 2.4.16
NIST: https://nvd.nist.gov/vuln/detail/CVE-2025-47904
CVSS:
Severity:
Credits: Dario Emilio Bertani, Raffaele Bova, Andrea Sindoni, Simone Bossi, Antonio Carriero, Marco Manieri, Vito Pistillo, Davide Renna, Manuel Leone, Massimiliano Brolli
The upgrade package is not signed through an asymmetric encryption scheme, allowing a malicious user to tamper and install an arbitrary filesystem.
Prerequisites: user knowledge of the decryption passwords and upgrade package structure.
Step-by-step instructions and PoC
Below are the evidences with the vulnerability details.
A malicious user able to decrypt the upgrade package as described in TIM_TP4100_010 - Hardcoded upgrade decryption passwords, can tamper with the filesystem and install a malicious version.
As show in the image below, once the file desc_enc is decrypted, the field md5 is used to check the integrity of the filesystem. By editing the md5 and encrypting the desc_enc file with the hardcoded password, the filesystem is accepted and properly installed.
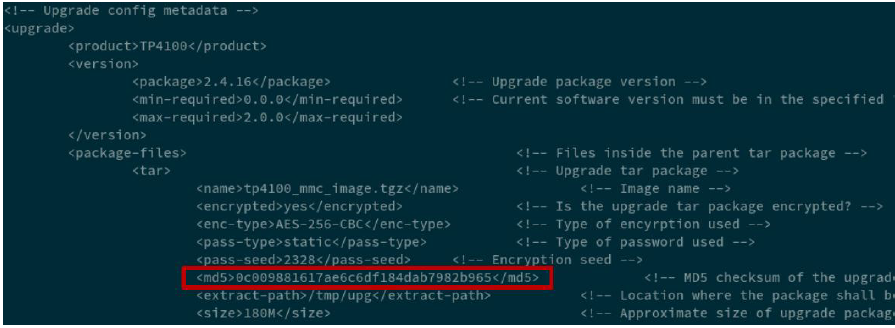
Figure 1 - Proof of Concept
Security Impact
An unsigned upgrade package lacks cryptographic validation, making it vulnerable to tampering and unauthorized modifications. Without a digital signature (i.e. asymmetric encryption), attackers can alter the package, inject malicious code, or compromise system integrity.